⚒️ MEET OUR TEAM ⚒️
Josh Block
Senior at Mizzou, Josh has an emphasis in cybersecurity while also working at InfiniTech as a Microsoft 365 and Endpoint Engineer.

Luke Manary
Having an emphasis in software engineering and pursuing a career in front end/react dev, Luke continues his senior year Mizzou.

Oluwaseun Olaleye
Located in Chicago, Seun is a senior at Mizzou. Post graduation, he is looking into software engineering.

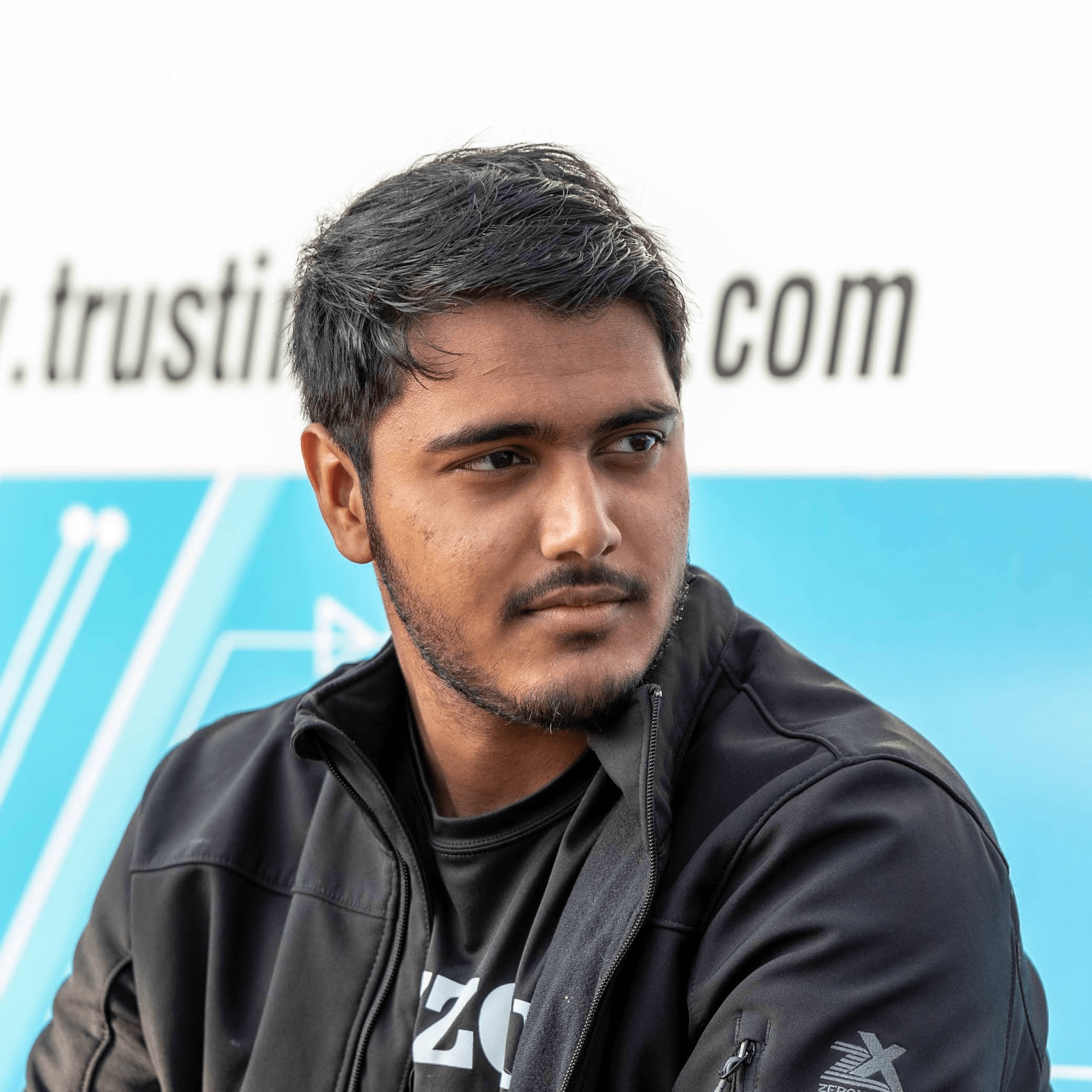
Dylan Reeves
Still unknown for future career, Dylan continues to work hard in his software engineering and cybersecurity classes to apply later in the workplace. Best drink to his opinion, Sprite.

Shelby Ward
Senior at Mizzou, Shelby is pursuing a career as a tech arch delivery analyst. Her degree emphasis is in software engineer. An enjoyable show of hers is Code Geass when not submitting homework.